Is Bitcoin Anonymous? Myths VS Reality and How BTC Transactions Are Tracked
The legend of Bitcoin's complete anonymity was born in its early years and persists to this day. However, the blockchain works differently: every transaction is recorded forever and is accessible to anyone. It is precisely this transparency that allowed US special services to seize over 173,000 BTC from Silk Road and recover part of the ransom after the Colonial Pipeline attack.
According to expert estimates, "shadow" addresses accounted for only 0.14% of transactions in 2025, but that still amounts to billions of dollars. So, Bitcoin is a network where a chain can be built for every address. In this article, we debunk popular myths about BTC and explain everything about its anonymity.
In this article:
- Myth 1. Bitcoin = complete anonymity
- Myth 2. Wallets are not linked to an identity
- Myth 3. The more transactions, the harder it is to track
- What "pseudonymity" means: the difference from anonymity
- How transactions are tracked on the blockchain
- Blockchain analytics tools: who cleans chains and how
- How special services catch criminals using BTC: real cases
- The role of exchanges and stablecoins in deanonymization
- How users improve privacy
- The future of privacy in crypto: where regulation and technology are heading
Myth 1. Bitcoin = complete anonymity
Early BTC users called it digital cash and compared it to physical currency: you hand over a bill, and the trail is lost. But in reality, it is the opposite. Any transaction (from a few dollars to billions) remains on the blockchain forever. Everything is visible: the amount, the date, and the sender's and receiver's addresses. Unlike banks, where data is private, the entire history of operations in the BTC network is open to any user. This means the blockchain is an ideal database for analysis.
A wallet address by itself does not contain a name, but it is enough to build connections. Analysts group addresses into clusters: if several inputs are involved in one transaction, they are almost always controlled by one person. User errors simplify the task: repeating amounts, identical time intervals for transfers, publishing data on forums — all these add pieces to the puzzle.
The result is obvious: Bitcoin is not anonymous, but merely pseudo-anonymous. It is a transparent network where the key to identity lies in off-chain data.
Myth 2. Wallets are not linked to an identity
At first glance, a Bitcoin wallet address does look like a random set of characters. It doesn't have a field for a name or phone number, but that doesn't mean an identity cannot be established through other means. In reality, it's simple: most leaks occur because of the users themselves.
Where identity linkage appears ⬇️
- Exchanges and exchangers with KYC. If you deposit or withdraw BTC through a platform with verification, your wallet address is automatically linked to your passport. Exchanges are required to store data and provide it to regulators upon request.
- Behavioral patterns. Repeating amounts, regular transfers, or identical transaction routes make a wallet recognizable.
- Publishing the address in open sources. Forums, social networks, donation requests.
- Transaction clustering. If several inputs are combined into one operation, they almost always belong to the same owner. This is how entire networks of linked wallets are built.
But the reality is this ⬇️
- Any wallet ↔ exchange link with a passport removes anonymity.
- Even without KYC, a couple of behavioral matches are enough for analysts to assemble the picture.
- The more transactions, the higher the chance of exposing the address in public data.
Myth 3. The more transactions, the harder it is to track
Many think that if you constantly move coins between different addresses, the trail is lost. But in reality, the more movement there is, the more clues there are for analysts.
Here is why frequent transfers don't help:
- Every step is recorded forever. There is no "delete history" function on the blockchain. Any transaction can be analyzed even years later.
- Clustering works more effectively. With a large number of operations, wallets are grouped into families. Algorithms see the patterns.
- Breaking up coins only simplifies the task. Many think that splitting an amount into dozens of small transfers makes it harder to track. In practice, it looks like the same source trying to hide, which immediately attracts attention.
- The history becomes longer and more transparent. Tracking a short chain of two transfers can be harder than a long one of twenty.
What "pseudonymity" means: the difference from anonymity
| Criterion | Pseudonymity | Anonymity |
| Identifier | Wallet address (set of characters) | Absence of any identifiers |
| Transaction transparency | All transactions are visible on the blockchain | Transactions are untraceable |
| Link to identity | Appears via KYC, address publication, or leaks | None, identity cannot be established |
| Traceability | High | Practically impossible |
| Privacy level | Relative (depends on user behavior) | Absolute (identification excluded) |
How transactions are tracked on the blockchain
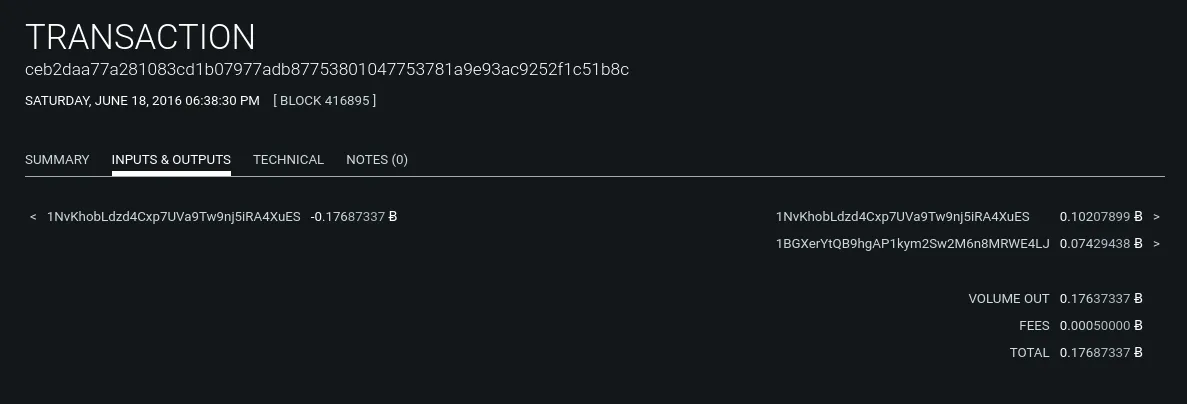
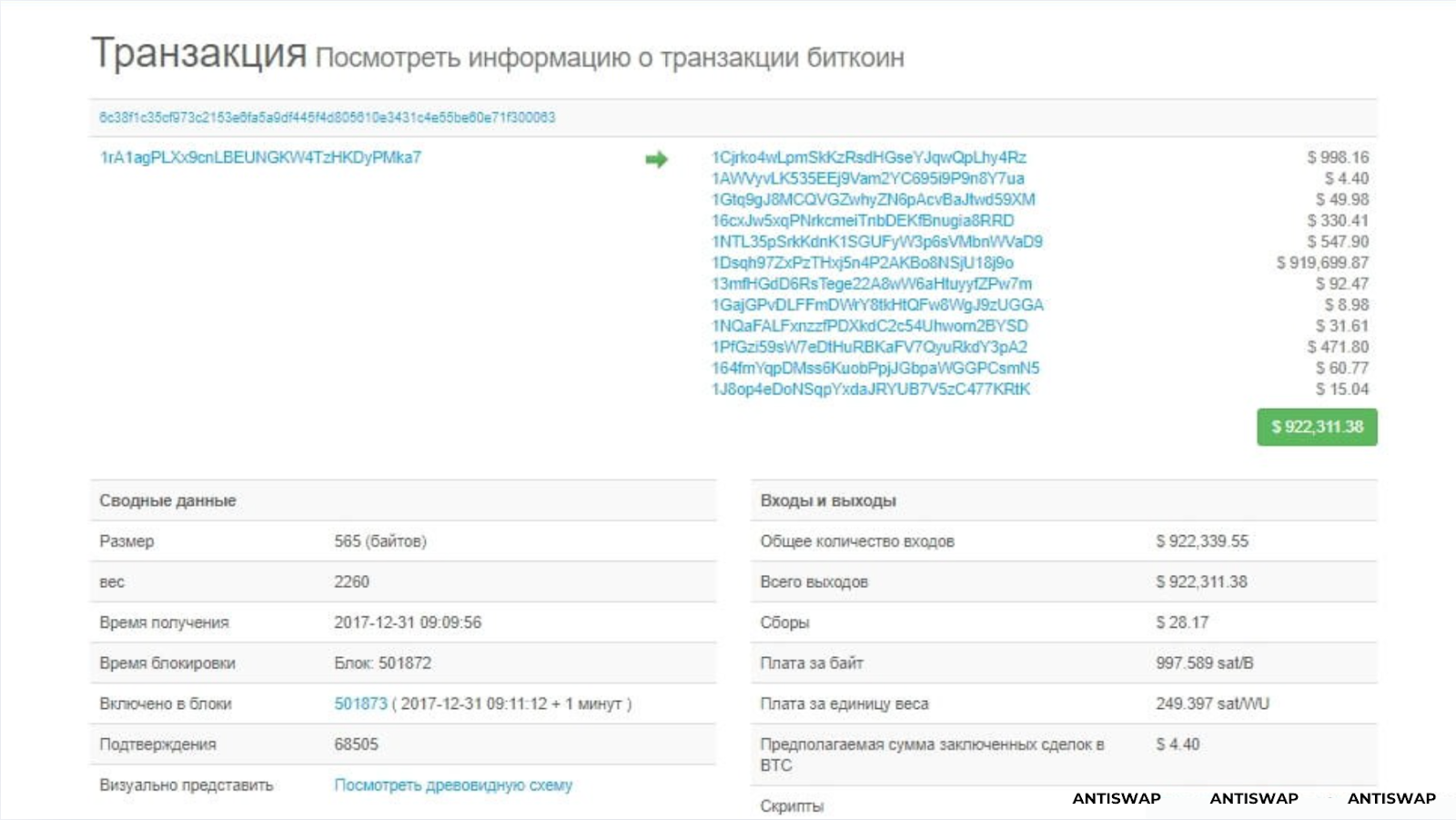
Technically, it works like this: every transaction contains inputs and outputs. An "input" is the address from which funds came, and an "output" is the one they go to. When transferring Bitcoins, a digital chain of ownership is effectively signed: who received funds from whom.
A transaction graph analysis method is used for tracking. If you imagine all addresses and transfers as a network, you get a map where nodes are connected by lines. As the same user employs multiple addresses, the chain of connections becomes increasingly transparent.
To make it clearer, here is a simplified scheme:
- All transactions are open and verifiable.
- Every transfer connects addresses into a single chain.
- Any entry point (exchange, service, store) can link an address to an identity.
- From there, the connection is traced both to the original wallet and to subsequent transfers.
It is precisely because of this openness that Bitcoin is often called the "most transparent" payment system in the world. Beginners mistakenly believe that a set of characters in an address guarantees invisibility. In reality, it is just a pseudonym that can be linked to a real person at any moment.
Blockchain analytics tools: who cleans chains and how
The fact that Bitcoin transactions are public does not in itself make them understandable. To turn a set of addresses from long strings into meaningful schemes, specialized blockchain analytics tools have emerged. These services build transfer graphs, mark suspicious clusters, and allow for finding connections between wallets.
Major market players:
- Chainalysis — one of the first and most famous tools. Used by exchanges, banks, and law enforcement agencies worldwide. The system can classify addresses by type (exchange, mixer), track the movement of funds between them, and build transfer chains in real-time.
- Crystal Blockchain — a service with Russian roots, popular in CIS countries. It is used by crypto exchanges and companies to check counterparties so they don't accept "dirty" coins. Crystal builds visual maps of asset movement and allows for assessing the risk level of a transaction.
- Elliptic — a British company working with banks and regulators. The main focus is on identifying suspicious patterns. Elliptic has an extensive database of connections between addresses.
- TRM Labs — a tool for compliance checking. It helps businesses understand if a partner has links to money laundering, fraud, or sanctions evasion.
To understand their capabilities, it is enough to look at the main functions:
| Capability | What it provides |
| Address clustering | Combining dozens of wallets into one "identity" based on usage patterns |
| "Dirty" coin labeling | Marking assets suspected of involvement in crimes |
| Graph visualization | Clear diagrams of BTC movement between addresses |
| Risk assessment | Automatic suspicion rating for transactions |
| Real-time monitoring | Tracking transfers at the very moment they occur |
In essence, these tools have turned the blockchain into a transparent ecosystem where the path of any coin can be traced. In the crypto industry, they have already become the standard. No serious exchange operates without them: the risk of facing regulatory claims is too high.
How special services catch criminals using BTC: real cases
The algorithm is usually the same: they analyze the transfer graph, look for nodes where money enters exchanges or services with KYC, and then request data.
❗️First example — Silk Road. On this platform, users conducted anonymous deals, and it was through this site that Bitcoin first gained the reputation of a shadow currency. In 2013, US authorities shut down the site and confiscated about 173,991 BTC from its creator. This story showed that even complex schemes leave traces that can be linked to real operational activity.
❗️Second famous case — the attack on Colonial Pipeline in 2021. After the incident, the company transferred about 75 Bitcoins to the attackers to restore system operations. Later, law enforcement was able to recover part of these funds: the Department of Justice announced the seizure of 63.7 BTC.
According to the investigation, specialists analyzed transactions on the blockchain and, with the help of partners from private analytical firms, tracked the path of the coins.
The role of exchanges and stablecoins in deanonymization
The key point is crypto exchanges. Most large platforms operate under KYC/AML rules: they require a passport, a selfie, and sometimes even proof of residence. Without this, you cannot deposit or withdraw assets. This means that as soon as coins enter an exchange, they can be linked to a specific person.
Exchanges cooperate with analytical companies like Chainalysis or Crystal, which check transactions for "purity." If coins came from a mixer, they may be marked as risky. Sometimes the account is blocked until verification, and in cases of serious suspicion, client data may be handed over to law enforcement.
Stablecoins play an equally important role. It would seem they are no different from Bitcoin in terms of transfer. But the difference is that stablecoins are centralized: the issuer (e.g., Tether or Circle) has the ability to block addresses upon request from regulators. If funds come under suspicion, they can be frozen right in the wallet.
Thus, exchanges and stablecoins have become the main points of deanonymization: here, digital addresses turn into real identities, and the movement of funds ceases to be "shadowy" and becomes part of the official financial system.
How users improve privacy
Users sometimes look for ways to make their transfers less noticeable. There are various technologies and approaches, each with its own features and risks. Below is a brief overview of methods, without instructions on how to use them.
- Input mixing/mixers. Here, funds are blurred among many others and then returned to different addresses. This is done to break the direct link between the source and the recipient.
At the same time, centralized mixers require trust (the operator can steal money or keep log data); many mixers come under the attention of regulators and are blocked. Also, it is worth considering that using mixers increases the probability that subsequent transactions will mark the funds as "risky." - Joint transactions like CoinJoin. Several users jointly form one transaction with multiple inputs and outputs so that it is impossible to unambiguously match whose input belongs to whose output.
- Lightning Network. Two users open a channel between each other. Then they can send as many payments as they want within that channel, and they do not enter the global registry. Only two operations are visible on the blockchain: when the channel was opened and when it was closed. Thanks to this, transfers are fast, fees are almost zero, and small payments are hidden from direct chain analysis.
But there are nuances. The very fact of opening and closing a channel is still recorded publicly. Furthermore, the routes that transfers take within Lightning can highlight technical data. If funds need to be withdrawn back into traditional financial systems, privacy no longer saves you: exchange on a platform requires KYC. Plus, the Lightning ecosystem is not equally developed everywhere, which affects convenience and the set of features. - Privacy coins (ZCash, Monero, Dash). Protocols like Monero use ring signatures, stealth addresses, and confidential transactions to make amounts, senders, and receivers untraceable at the on-chain level. A high level of privacy is guaranteed at the protocol level.
Along with their effectiveness, privacy coins attract increased attention from regulators and banks. Many centralized exchanges limit work with such assets or require additional checks.
Sometimes people try to exchange privacy coins through exchangers. This is a normal practice, but it has its nuances and risks that are worth remembering.
Important! Some exchange platforms block transfers, citing anti-money laundering (AML) rules. In such cases, the user may be presented with a long list of requirements: provide personal documents, screenshots of correspondence, or even utility bills.
It is more convenient to look for verified and safe exchangers through specialized aggregators like AntiSwap. Here, every site has a label: "honest," "neutral," or "scam." This helps to immediately filter out dubious platforms and choose a reliable option.
How does the exchange process work? We'll tell you now.
1. First, the user selects the necessary exchange direction.
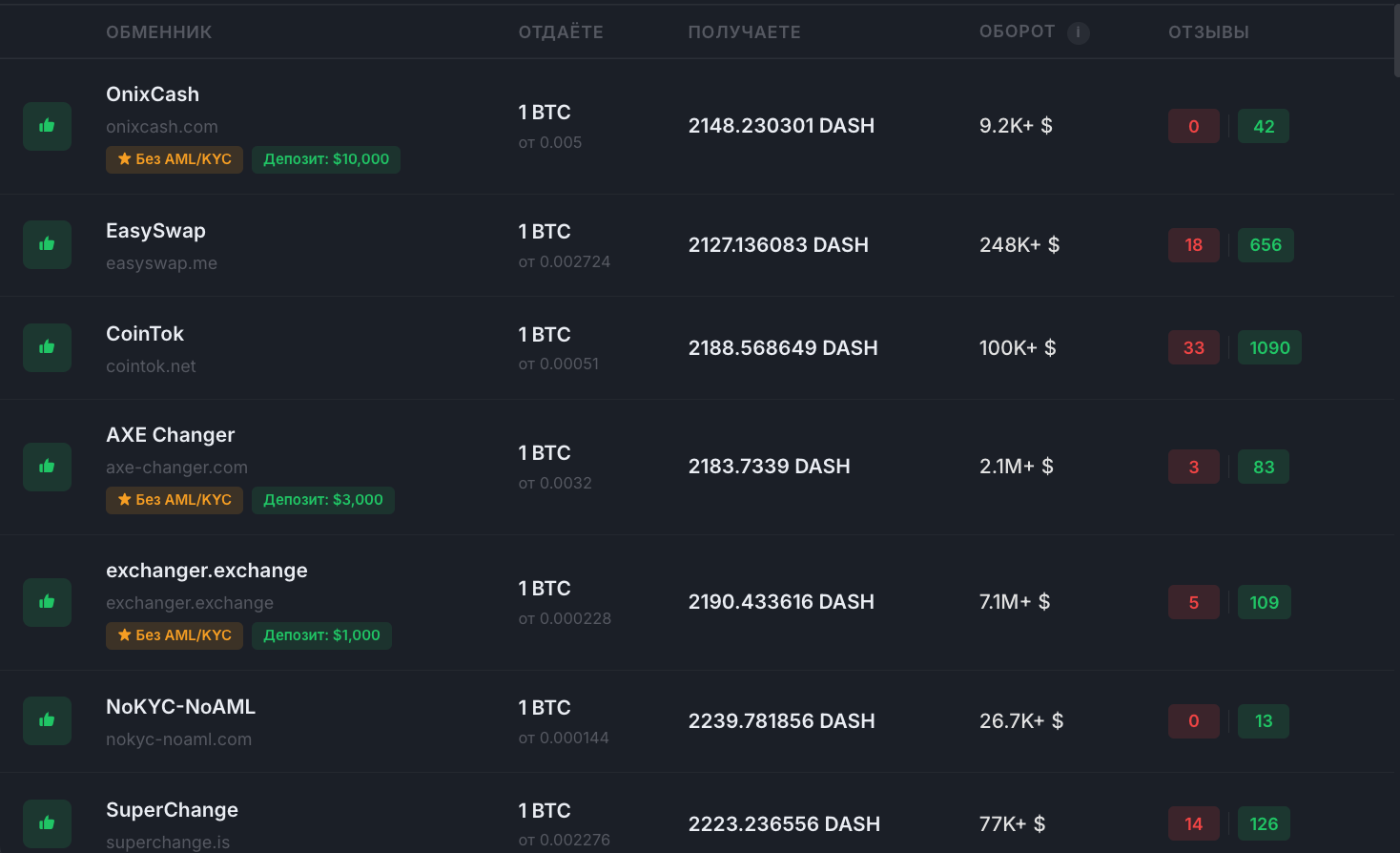
2. Next, they view all suitable crypto exchanger options.
When analyzing exchange platforms, one usually pays attention to several factors:
- Status. On AntiSwap, every platform has a label reflecting its reputation. The "honest" label indicates stable operation without serious incidents. Some exchangers are additionally marked with a star — this is a sign of increased trust and the presence of an insurance deposit.
- Rate. Platforms may offer different exchange conditions, so this parameter often becomes decisive when comparing services.
- Reviews. User ratings help understand how the platform resolves disputes. The presence of complaints about delays or blocks may indicate potential risks.
3. After choosing a platform, the user is redirected to the official website of the exchanger. There, the terms of operation, application forms, and information about fees are usually posted. The transaction processing time depends on the service.
No technology provides complete anonymity. Nevertheless, the community discusses techniques that help increase the level of confidentiality without breaking the law.
- Address separation. Users sometimes create separate addresses for different purposes so as not to mix personal and public transfers.
- Separate wallets. Some prefer to keep different wallets for savings and daily operations to simplify the control of fund movement.
- CoinJoin and similar solutions. There are wallets that support joint transactions. Such tools are discussed as a way to increase privacy, but it must be taken into account that exchanges and compliance departments may view them with caution.
- Gray schemes for fiat withdrawal are considered risky. Using verified exchangers is a compromise between simplicity and privacy.
The future of privacy in crypto: where regulation and technology are heading
The topic of privacy in cryptocurrency continues to be one of the hottest. On one hand, technologies are developing: new protocols are appearing, Lightning capabilities are expanding, and mixing schemes and privacy coins continue to improve.
On the other hand, pressure from regulators is growing. In many countries, KYC and AML rules require checking large operations on exchanges and with stablecoins. Suspicious transfers are recorded and, if necessary, handed over to law enforcement. International initiatives (FATF, EU, USA) are gradually building unified "travel rule" standards, where transparency and traceability remain mandatory.
As blockchain analytics becomes more accurate, simple attempts to mask transactions become less effective. Therefore, the future of privacy will be built on a balance: legal solutions for data protection, new protocols that provide privacy without breaking the law, and, in parallel, stricter regulation.
This material is for informational purposes only and does not encourage the circumvention of laws or the use of cryptocurrencies for illegal purposes. All recommendations concern only legal and responsible use.